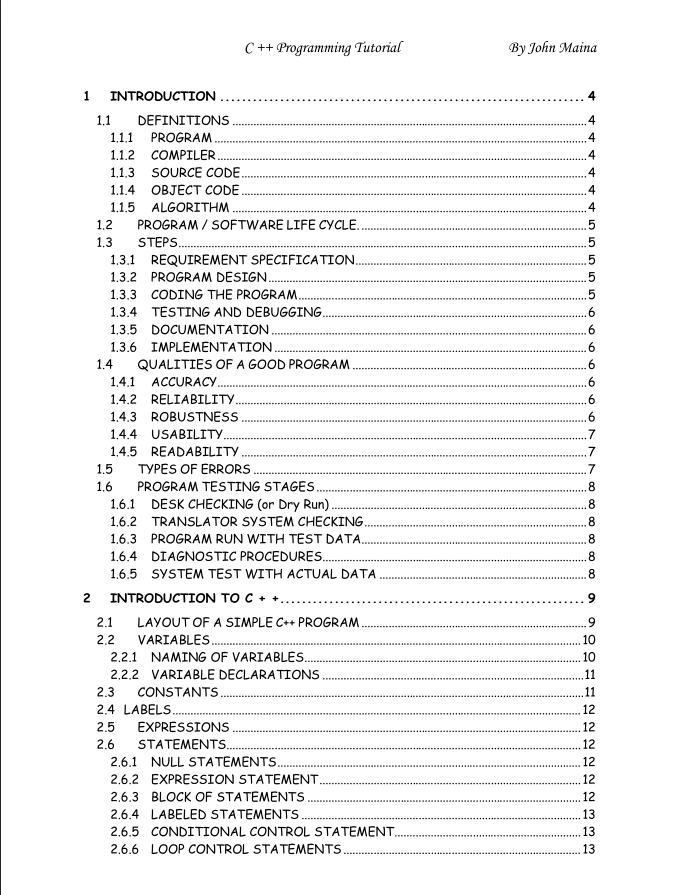
C ++ Programming Tutorial By John Maina
| Institution | JKUAT |
| Course | Information Technolo... |
| Year | 1st Year |
| Semester | Unknown |
| Posted By | Jeff Odhiambo |
| File Type | |
| Pages | 99 Pages |
| File Size | 461.91 KB |
| Views | 5339 |
| Downloads | 1 |
| Price: |
Buy Now
|
Description
C Language Overview
This chapter describes the basic details about C programming language, how it emerged,
What are strengths of C and why we should use C.
The C programming language is a general purpose, high level language that was
originally developed by Dennis M. Ritchie to develop the UNIX
operating system at Bell Labs. C was originally first implemented on the DEC PDP
11 computer in 1972.
In 1978, Brian Kernighan and Dennis Ritchie produced the first publicly available
description of C, now known as the K&R standard. The UNIX operating system, the C compiler, and essentially all UNIX applications programs have been written in C.
The C has now become a widely used professional language for various reasons.
Easy to learn
Structured language
It produces efficient programs.
It can handle low level activities.
It can be compiled on a variety of computer platforms.
Facts about C
C was invented to write an operating system called UNIX.
C is a successor of B language, which was introduced around 1970.
The language was formalized in 1988 by the American National Standard
Institute.(ANSI).
The UNIX OS was totally written in C by 1973
Below is the document preview.
RISK MANAGEMENT
A risk assessment is a quantitative or qualitative process that deals with the identification of possible risks and their impacts, and provides measures to be taken to reduce those risks. When a risk assessment is complete, risk mitigation is performed to implement risk control measures to minimize the risk to an acceptable level.
7 Pages
480 Views
0 Downloads
601.92 KB
COMPUTER CRIME AND FRAUD
Trending!
Computer crime is an act performed by a knowledgeable computer user, sometimes referred to as a hacker that illegally browses or steals a company's or individual's private information. In some cases, this person or group of individuals may be malicious and destroy or otherwise corrupt the computer or data files.
16 Pages
3587 Views
0 Downloads
217.02 KB
RESEARCH METHODS TERMINOLOGIES
Trending!
Any information on the structure, content, and layout of a data set. The codebook typically provides background on the project, describes the data collection design, and gives detailed information on variable names and variable value codes.
17 Pages
4299 Views
0 Downloads
357.31 KB
AMT 209: Editing for Print Media
Trending!
Copyright pertains to protection of intellectual property. The law protects the product of intellect. Property is, therefore not just physical. It can also be intellectual.
2 Pages
6265 Views
0 Downloads
75.16 KB
ATM 202/3: The Newsroom: Gatekeepers, Perceptions and Expectations
The newsroom is the central hub in the news production chain. Every major decision rotates around the newsroom. It is the heart of everything in the gathering, processing and dissemination of information. All the crucial decisions begin and end here.
4 Pages
90 Views
0 Downloads
402.89 KB
SCS 409: IT and Society
Trending!
Information technology (IT) is the study, design, development, implementation, support or maintenance of computer-based information systems.
70 Pages
3931 Views
0 Downloads
1.36 MB
DDS 101: INTRODUCTION TO DEVELOPEMENT STUDIES
Trending!
Examines the patterns, practices, policies and theories associated with inequalities in world development. The discipline pays particular attention to the relationships between “developed” and “developing” societies.
90 Pages
4519 Views
1 Downloads
1.07 MB
UCI 202: COMPUTER BASED INFROMATION SYSTEM
Trending!
This course presents the fundamental methodology and process for the analysis and design of computer based information system.
59 Pages
5901 Views
0 Downloads
707.18 KB
System Analysis and Design
System is an orderly grouping of interrelated and interdependent components linked together according to a plan to achieve a specific common goal.
32 Pages
281 Views
0 Downloads
327.91 KB
COMPUTER NETWORKS
A computer network, is a collection of computers and other hardware components interconnected by communication channels that allow sharing of resources and information.
14 Pages
351 Views
0 Downloads
904.58 KB