Environmental revision question(QUESTION & ANSWER)
| Institution | TVET |
| Course | DIPLOMA IN SOCIAL WO... |
| Year | 1st Year |
| Semester | Unknown |
| Posted By | stephen oyake rabilo |
| File Type | |
| Pages | 9 Pages |
| File Size | 175.27 KB |
| Views | 4492 |
| Downloads | 0 |
| Price: |
Buy Now
|
Description
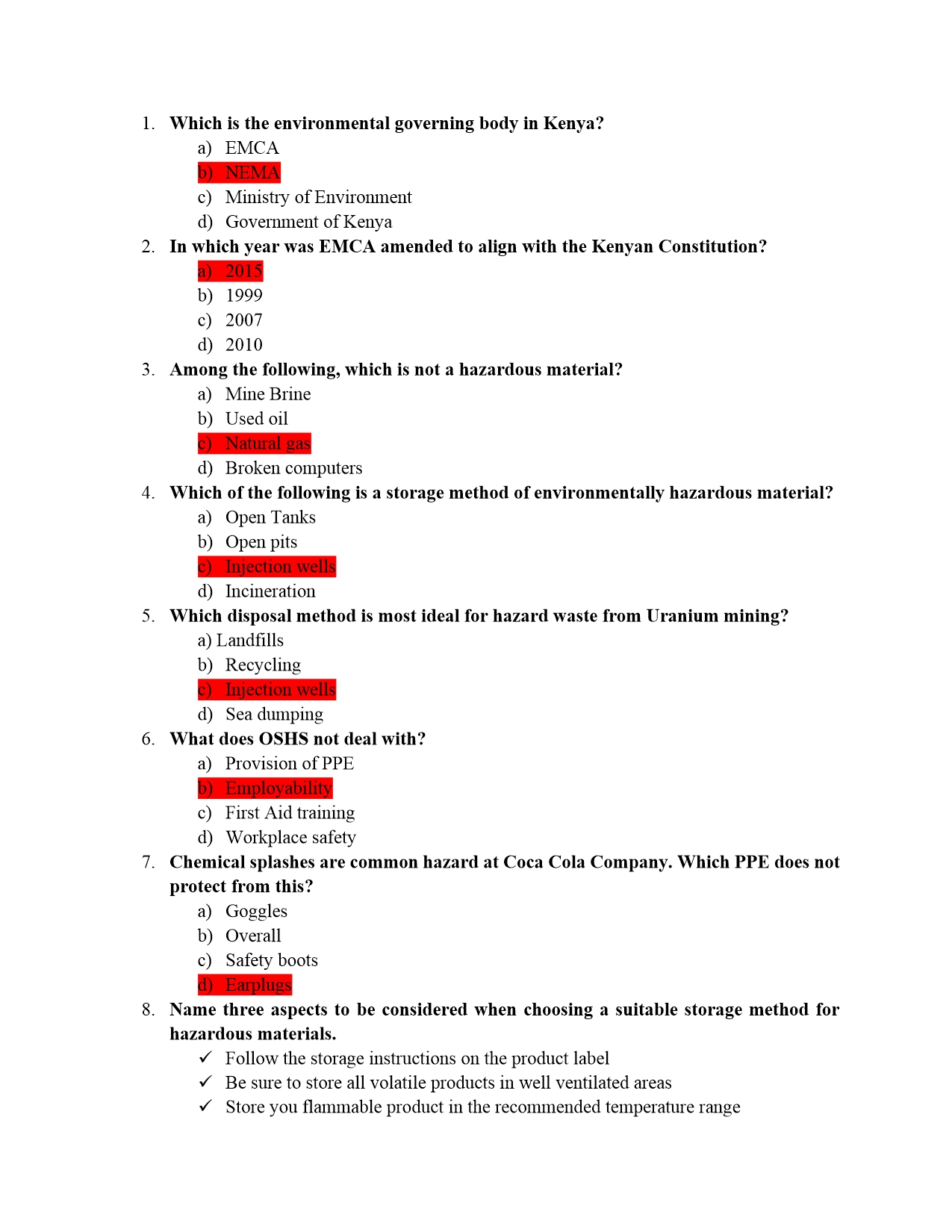
1. Which is the environmental governing body in Kenya?
a) EMCA
b) NEMA
c) Ministry of Environment
d) Government of Kenya
2. In which year was EMCA amended to align with the Kenyan Constitution?
a) 2015
b) 1999
c) 2007
d) 2010
3. Among the following, which is not a hazardous material?
a) Mine Brine
b) Used oil
c) Natural gas
d) Broken computers
4. Which of the following is a storage method of environmentally hazardous material?
a) Open Tanks
b) Open pits
c) Injection wells
d) Incineration
5. Which disposal method is most ideal for hazard waste from Uranium mining?
a) Landfills
b) Recycling
c) Injection wells
d) Sea dumping
6. What does OSHS not deal with?
a) Provision of PPE
b) Employability
c) First Aid training
d) Workplace safety
7. Chemical splashes are common hazard at Coca Cola Company. Which PPE does not
protect from this?
a) Goggles
b) Overall
c) Safety boots
d) Earplugs
Below is the document preview.
PSY 211: GUIDANCE AND COUNSELLING
Trending!
Guidance means of helping individuals to understand and use wisely the educational, vocational and personal opportunities they have as a form of systematic assistance in achieving satisfactory adjustment to school and to life in general.
4012 Views
1 Downloads
608.55 KB
Ethics for IT Workers and IT Users
Trending!
Ethics in Information Technology, Fourth Edition
3629 Views
0 Downloads
710 KB
Computer Legal and Ethical Issues
Trending!
The focus is on technical approaches to the detection, prevention, and recovery from
computer and network attacks. One other tool is the deterrent factor of law enforcement. Many types of computer attacks can be considered crimes and, as such, carry criminal sanctions. This section begins with a classification of types of computer crime and then looks at some of the unique law-enforcement challenges of dealing with computer crime.
3942 Views
0 Downloads
113.27 KB
Law of Agency
Trending!
It is a general principle of contract law that only the parties to the contract acquire rights and liabilities under it. A well recognized exception to this general rule is the concept of agency.
12 Pages
4092 Views
1 Downloads
211.25 KB
PP1 TERM 3 SCHEMES OF WORK- ART
Trending!
UPDATED ARTS SCHEMES OF WORK TERM3 PP1
12 Pages
5514 Views
0 Downloads
837.93 KB
CRE SCHEMES OF WORK PP1 TERM3
Trending!
UPDATED CRE SCHEMES OF WORK PP1 TERM3
9 Pages
4598 Views
0 Downloads
868.76 KB
ENVIROMENTAL ACTIVITIES SCHEMES OF WORK PP1 TERM3
Trending!
UPDATED ENVIRONMENTAL ACTIVITIES SCHEMES OF WORK PP1 TERM3
18 Pages
4413 Views
0 Downloads
873.3 KB